Endpoint security solutions stop at the device. Threats don't.
NordLayer controls who can access your network and private apps. CrowdStrike Falcon Enterprise detects and stops endpoint threats that get through. Together, they reduce breach risk and contain attacks before they spread.
14-day money-back guarantee
15,000+ businesses trust NordLayer to keep their networks secure and under control
SOC 2 compliant
ISO 27001 compliant
PCI-DSS compliant
HIPAA compliant
CrowdStrike extends that trust with industry-leading enterprise endpoint security
Gartner Magic Quadrant Leader
Named a Leader for the sixth consecutive year in the 2025 Gartner® Magic Quadrant™ for Endpoint Protection Platforms.
Enterprise-grade regulatory compliance
A SOC 2 Type II certified platform that’s built for regulated industries at scale with 99.99% uptime guaranteed.
Pressure-tested with perfect scores
100% detection, 100% protection, zero false positives in the 2025 MITRE ATT&CK® Enterprise Evaluations.
KNOW THE RISKS
The state of cybercrime has fundamentally changed
In 2025, threat actors stopped choosing between network and endpoint attacks. They use both. Your defense should too.
40%
of vulnerabilities exploited by China-nexus adversaries targeted edge devices like VPNs and firewalls.
82%
of detections were malware-free, with attackers using valid credentials to breach networks instead.
42%
increase in zero-day exploits targeting internet-facing network infrastructure.
29 mins
is the average breakout time from initial breach to lateral movement across your network.
FEATURES
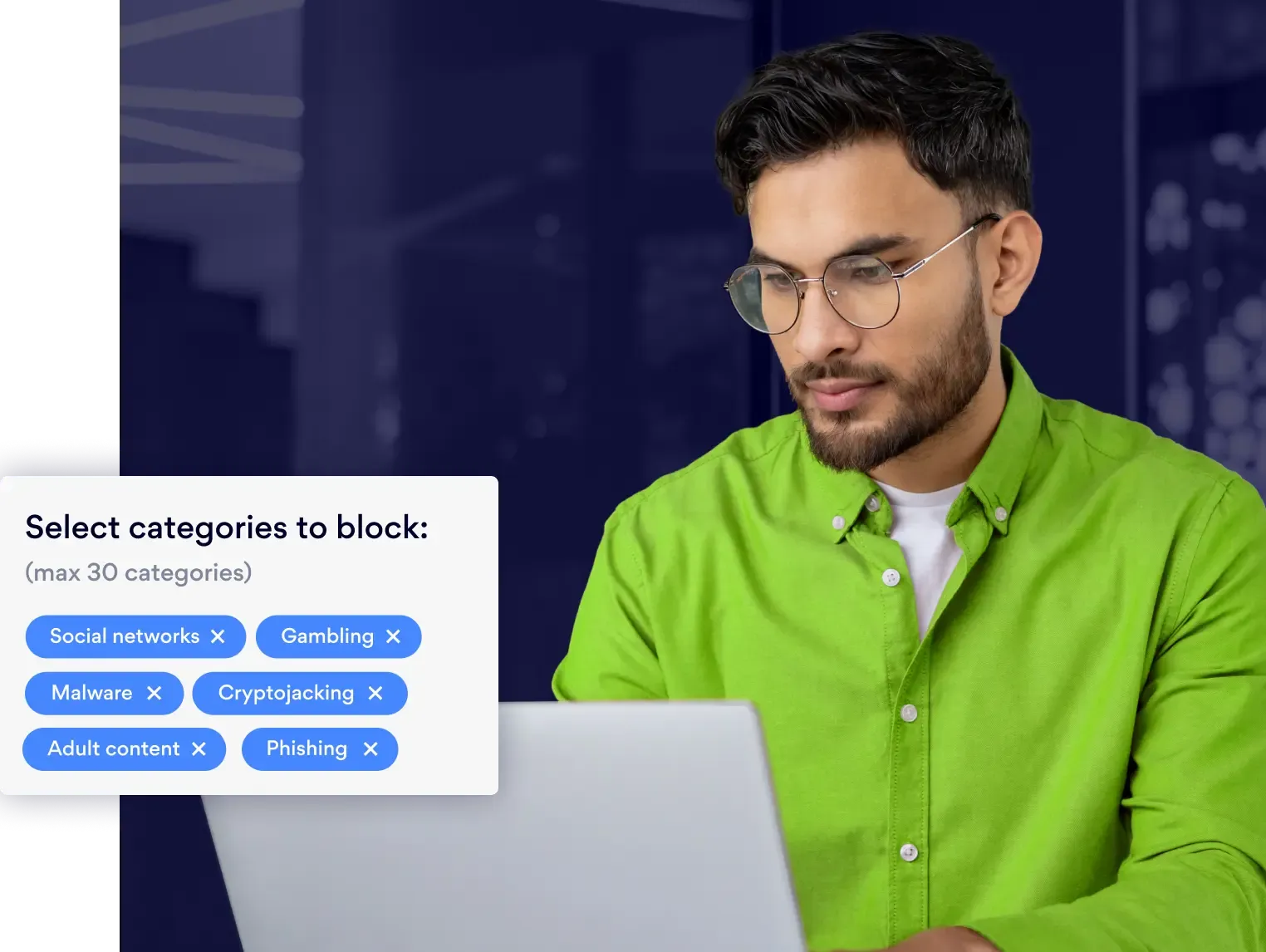
Everything your team needs to secure access and endpoints
Start using CrowdStrike Falcon Enterprise with NordLayer
BENEFITS
What do you get when network and endpoint security work together?
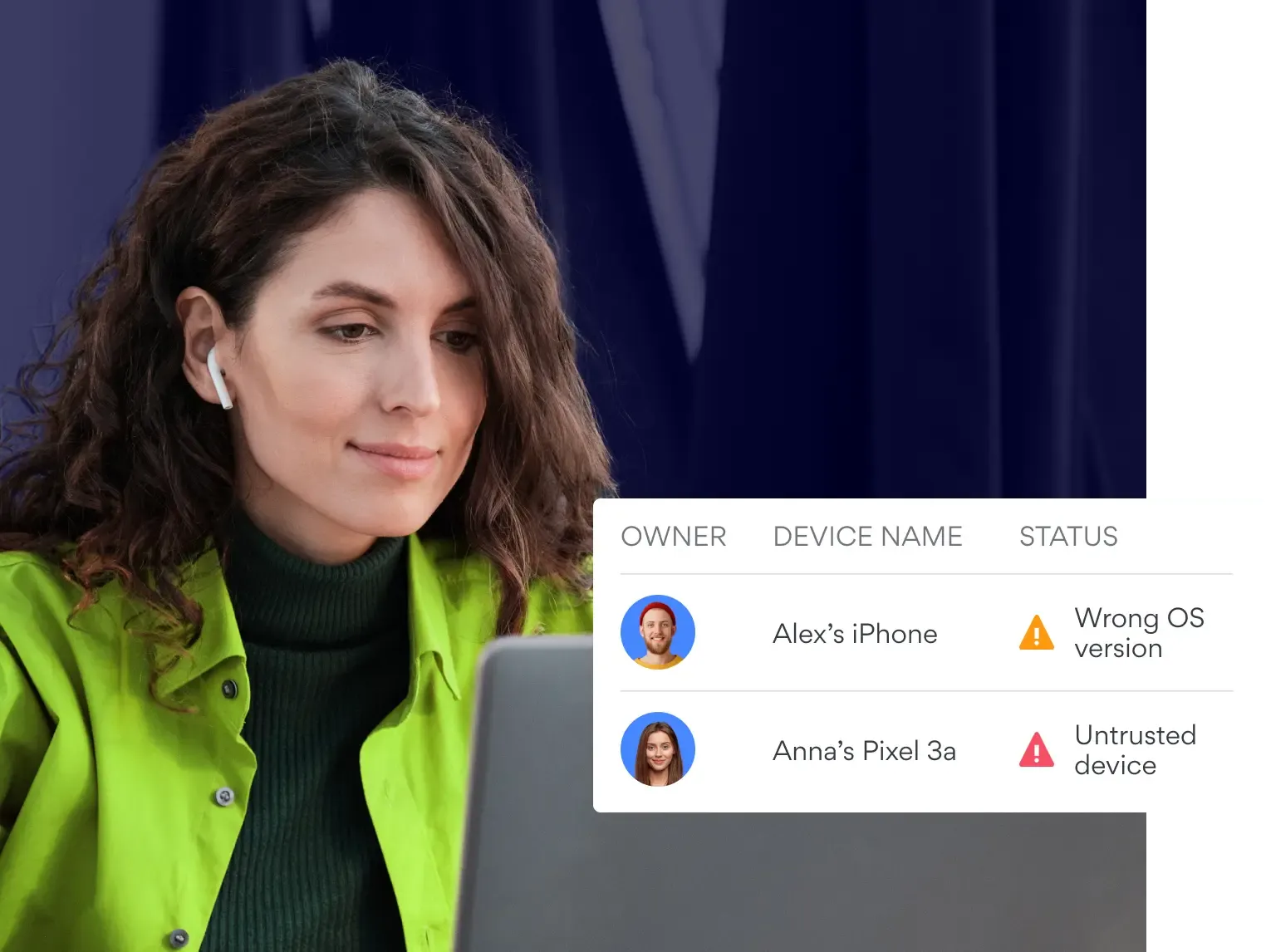
Close the gap between network access and endpoint protection
Attackers exploit the seam between tools that don't share context. This bundle pairs NordLayer's access controls with CrowdStrike Falcon's Enterprise endpoint protection so threats can’t hide.
Contain breaches before they spread across your organization
Average breakout time is 29 minutes. Endpoint isolation and network segmentation work together to stop lateral movement before one compromised device becomes ten.
Simplify audits and compliance readiness
NordLayer logs who connected. CrowdStrike records what happened on every endpoint. Together, you get the evidence auditors need without stitching reports from separate tools.
Reduce tool sprawl and speed up deployment
Get network access and endpoint protection through a single checkout with fewer vendors to evaluate, faster procurement, and a simpler path to full coverage.
GETTING STARTED
How to activate your enterprise bundle
NordLayer secures your network access. CrowdStrike Falcon Enterprise protects your endpoints. Here's a simple guide to get both running.
Set up NordLayer network access
Create your NordLayer account and configure network access policies for your team, devices, and locations.
Add CrowdStrike Falcon Enterprise
Purchase your CrowdStrike Falcon Enterprise license through the bundle and deploy the lightweight agent across your endpoints.
Start protecting both layers
Your network access controls and endpoint detection and response (EDR) are live. Monitor, manage, and respond from both platforms.
Ready to close the gap between your network and your endpoints?
Talk to our team about bundling NordLayer with CrowdStrike Falcon Enterprise for your organization.
RESOURCES
Get more insights on enterprise endpoint security
Additional info
Frequently asked questions
An endpoint security solution is software that protects devices like laptops, desktops, servers and mobile phones from cyber threats. Modern endpoint security software goes beyond traditional antivirus to include threat detection, behavioral analysis, and automated response. For organizations managing large device fleets, an enterprise endpoint security solution like CrowdStrike Falcon provides centralized visibility and control across every endpoint in the network.
Endpoint security is the practice of securing every device that connects to your organization's network. This includes protection against malware, ransomware, insider threats, and credential-based attacks. Enterprise endpoint protection typically combines data loss prevention (DLP), extended detection and response (XDR) and other controls in a single agent, giving security teams the ability to monitor, investigate, and contain threats across all endpoints in real time.
Common examples of endpoint security include next-gen antivirus, endpoint detection and response (EDR), extended detection and response (XDR), device encryption, and application control. CrowdStrike endpoint security is one example, using a lightweight agent for real-time threat detection and response. When paired with network access controls like NordLayer, organizations add a second layer that verifies who and what connects to the network before an endpoint is ever exposed.
The three main endpoint security types are:
1. Endpoint protection platform (EPP). Prevents known threats like malware and ransomware from executing on a device using signatures and AI-driven detection.
2. Endpoint detection and response (EDR). Monitors endpoint activity to detect advanced threats, insider threats, and suspicious behavior, then enables investigation and response.
3. Extended detection and response (XDR). Expands threat detection beyond endpoints to include network, cloud, and identity data in a single endpoint security platform.
An endpoint protection platform (EPP) prevents known threats at the endpoint before they execute. Think antivirus, but smarter. An endpoint detection and response (EDR) assumes some advanced threats will get through and focuses on threat detection, investigation, and response after the fact. An extended detection and response (XDR) extends that visibility beyond the endpoint to network, identity, and cloud layers.